Zero Trust - Secure Access to Corporate Resources
Zero Trust network deployed and maintained on WireGuard. Peer-to-peer encryption, SSO authentication, granular access policies. Works anywhere with an internet connection.
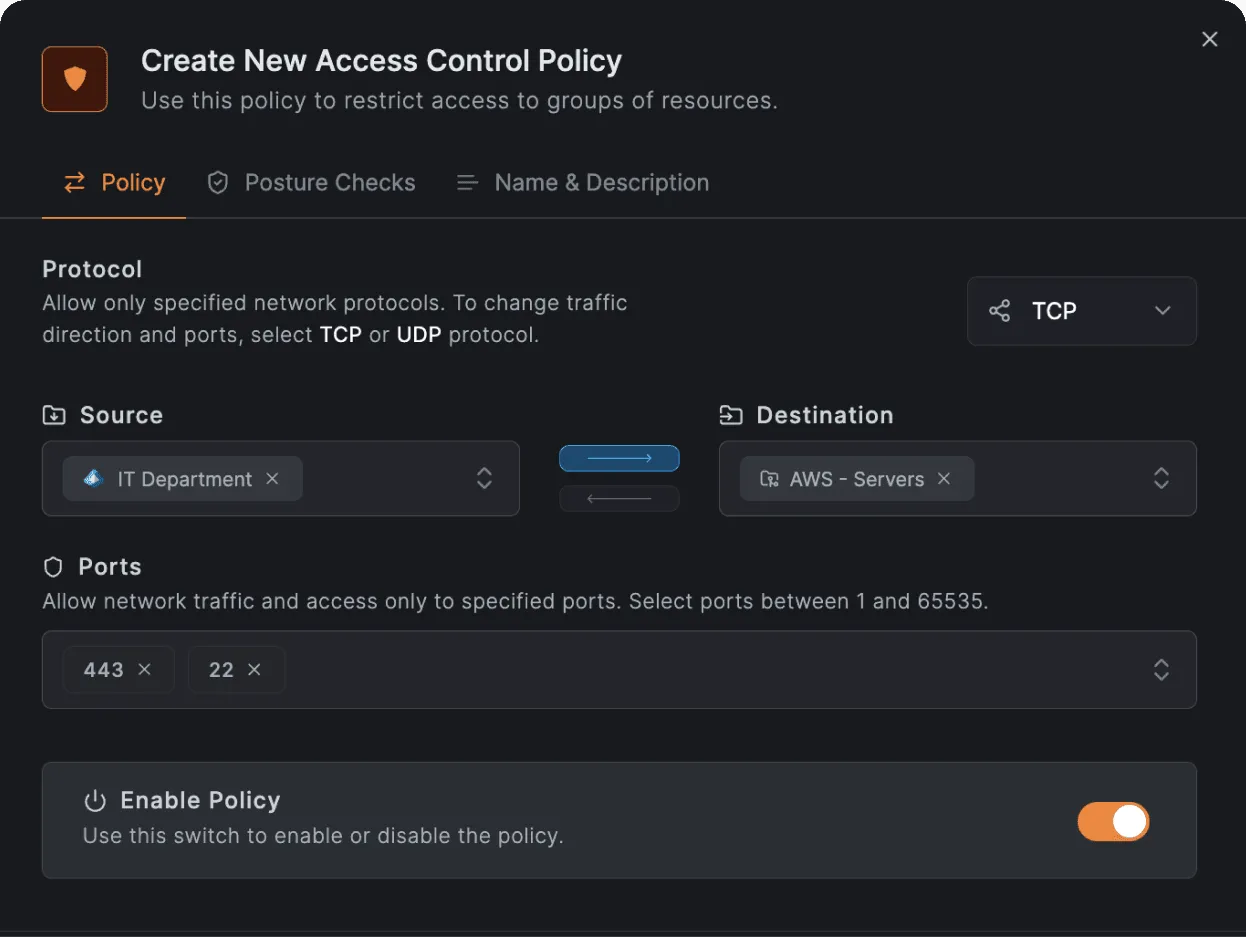
Granular access policies
Legacy VPN grants access to the entire corporate network. Zero Trust works differently: users access only the resources they need.
Policies created by group, role, and department. Changes applied instantly across the network. Access control operates down to the individual service and port level.
- Group-based segmentation
- Port-level policies
- Instant enforcement
- Peer-to-peer WireGuard
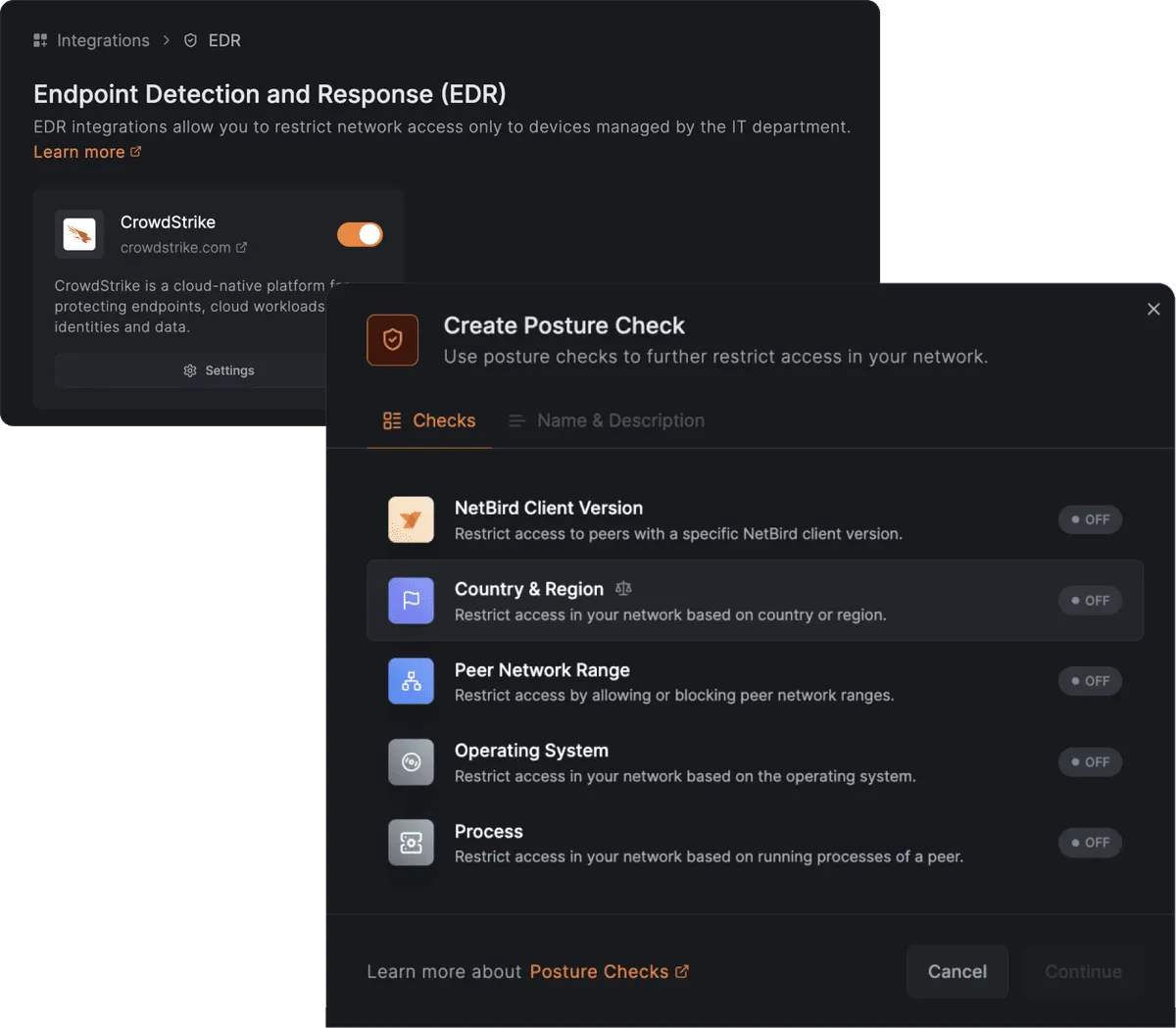
Device verification before connection
Network access granted only when the device meets corporate standards. Firewall enabled, antivirus current, OS updated.
Integrated with identity providers: Microsoft Entra ID, Google Workspace, or Okta. Users log in via SSO. Multi-factor authentication applied automatically.
- Device Posture Checks
- SSO / MFA
- Microsoft Entra ID
- Google Workspace
- Okta
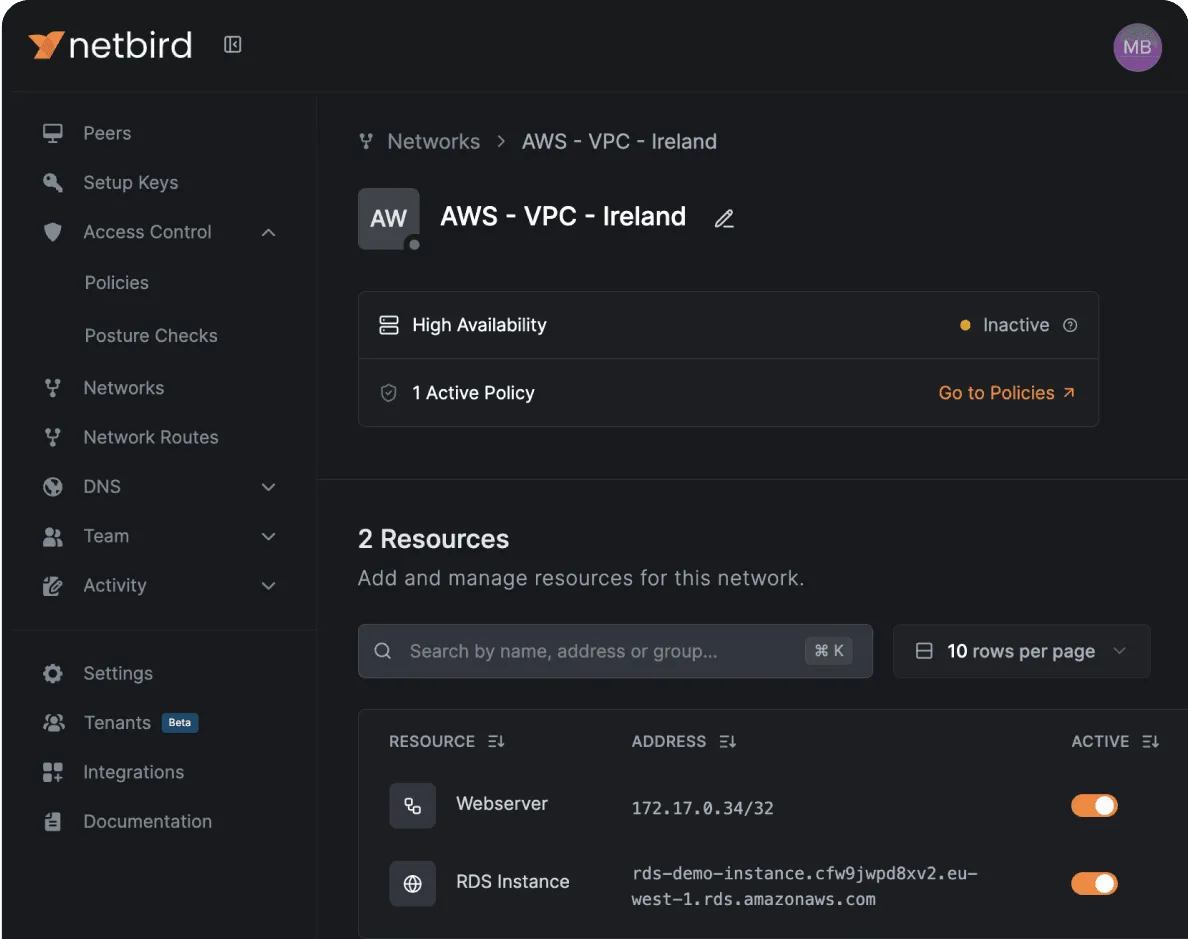
Centralized management
A single panel shows all devices, connections, and policies. Add users, block devices, change access rules - all in real time.
Private DNS zones let employees access internal services by readable names. Configuration applies automatically to all network participants.
- Device management. Connection status, agent version, OS, and last activity visible. Device blocked in one click.
- Private DNS. Internal services accessible by name: crm.company, gitlab.company. No additional device configuration required.
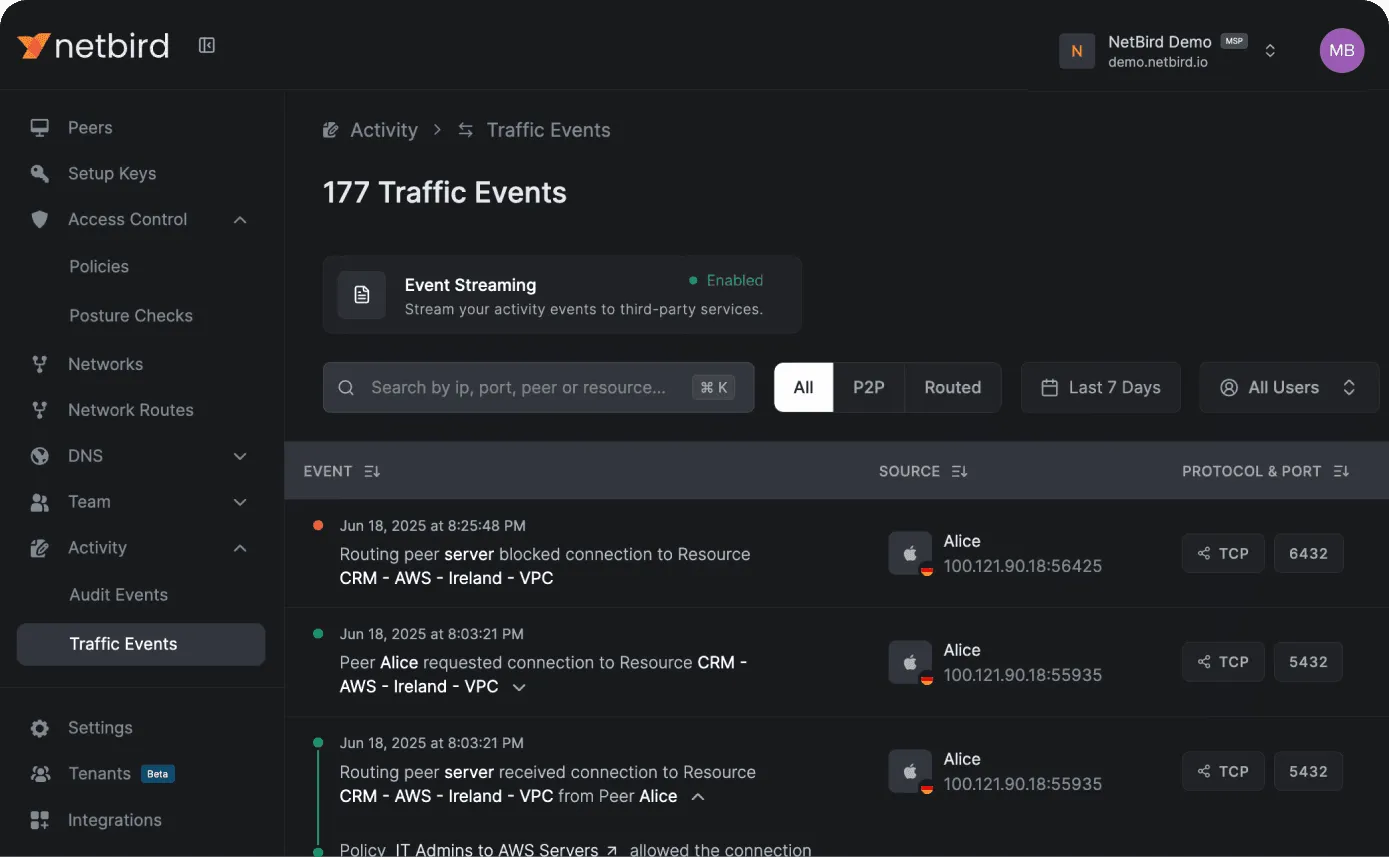
Complete activity log
All connections, policy changes, and admin actions recorded. Who accessed what, and when - in a single log.
Data forwarded to a SIEM system for real-time analysis. Full audit trail for information security compliance.
- Connection log
- Action audit
- SIEM integration
- Event export
Advantages - The modern VPN alternative
Zero Trust replaces legacy VPN solutions that are hard to scale and harder to control.
- No port opening. Devices connect without firewall or NAT configuration. Works through any internet connection, behind any provider.
- Instant onboarding. New employee gets access to corporate resources within minutes. Agent installed, SSO login completed.
- All platforms. Linux, Windows, macOS, iOS, Android, Docker, routers. A unified network for all device types.
- Scaling. New offices, cloud services, and remote employees connected without infrastructure changes.
- Self-hosted or cloud. Deploy on your own servers for full data control, or use cloud infrastructure.
- Open Source. Open source code. Full transparency, auditability, zero vendor lock-in.
How to start - Getting started
From first meeting to a working Zero Trust network - days, not weeks.
01
Current infrastructure audit
We analyze your existing network and VPN solutions. User groups, resources, and access policies defined.
02
Deployment and configuration
Platform deployed, identity provider integrated, policies created. Agents installed on devices.
03
Ongoing support
Policies managed, new users onboarded, platform updated. Availability and security maintained.